The faint hum of a server rack, the glow of multiple monitors—it’s the modern digital war room, and security is the ultimate battleground. But what if the most critical fortifications could be built with just three lines of Python?
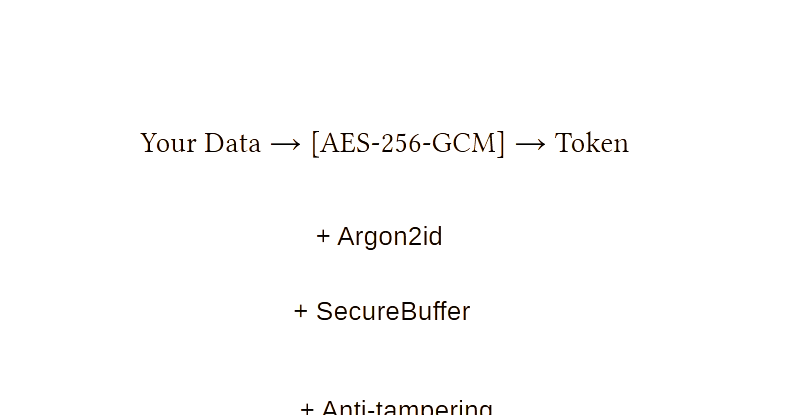
That’s the audacious promise of Flash512-Vanguard, a new open-source library aiming to democratize military-grade encryption for developers. Forget wading through NIST standards or wrestling with nonce management. This is about bringing the heavy artillery of cybersecurity—Argon2id, AES-256-GCM, and automatic memory wiping—down to the developer’s desktop, no PhD in cryptography required.
For too long, implementing strong encryption has felt like defusing a bomb blindfolded. The complexity is staggering: how do you manage those ephemeral keys? Is your nonce truly random? Did you securely zero out that sensitive data from RAM before the OS could page it out? A single slip-up, a tiny oversight, and your entire system, your users’ data, everything, can crumble into dust. It’s a constant tightrope walk over a digital abyss.
But here’s the thing: we’re living through a fundamental platform shift. AI is eating the world, yes, but beneath that seismic activity, we’re seeing a broader redefinition of what it means to build software. Security isn’t just a feature anymore; it’s the very bedrock upon which all future applications must be built. And Flash512-Vanguard seems to recognize this tectonic shift. It’s not just another library; it’s an attempt to embed a philosophy of hyper-security directly into the development workflow.
When Simplicity Meets Uncompromising Security
What’s truly striking about Flash512-Vanguard is its elegant simplicity. The core functionality boils down to three lines of code: protect, open, and verify. It’s almost jarringly straightforward. You feed your secret data and a password into protect, and out pops a token. To get it back, you reverse the process with open, using the same password. And verify? Well, that’s for checking if a token is legitimate without actually decrypting it – a neat trick for integrity checks.
This isn’t just about making things easy; it’s about making them right. The library use Argon2id as its primary Key Derivation Function (KDF). Now, for those not deeply embedded in the cryptographic trenches, think of a KDF as the meticulously trained guard dog for your encryption keys. Argon2id is particularly ferocious, being memory-hard and designed to make brute-force attacks, especially those leveraging GPUs and ASICs, economically unfeasible. It’s the gold standard, recommended by OWASP, and for good reason.
But what if Argon2id is overkill, or what if you need a fallback? Flash512-Vanguard has you covered with PBKDF2-HMAC-SHA512, configured with a hefty 100k iterations – still a serious deterrent. The primary encryption algorithm? AES-256-GCM, a NIST FIPS 197-approved standard known for its strong confidentiality and integrity. And the icing on this already delectable cake? Cryptographically random nonces for every operation, ensuring that even encrypting the same data twice yields entirely different ciphertext. Polymorphic output, they call it. No patterns to exploit.
“One mistake = total compromise.”
That stark statement from the project’s creator isn’t hyperbole; it’s the brutal reality of modern cybersecurity. Flash512-Vanguard’s mission is to eliminate that margin for error.
Beyond the Basics: Features That Make Developers Sleep Soundly
This library doesn’t stop at the core encryption. It dives deep into the nitty-gritty details that make security truly strong. Take automatic memory wiping. When you open an encrypted token, the sensitive data isn’t just loaded into memory; it’s loaded into a SecureBuffer. This specialized buffer is designed to securely zero out its contents—erasing the data—once it’s no longer in use. This is absolutely critical for preventing sensitive information from lingering in RAM, vulnerable to memory scraping attacks. It’s like having a self-destruct sequence for your secrets, built right in.
Key rotation, another enterprise-grade feature, allows you to change the master password without re-encrypting your entire dataset. This is a lifesaver for systems that require regular credential updates. The library also boasts an integrity module for tamper-checking at load time, adding another layer of defense against malicious interference.
And the output? It’s polymorphic. The same message, encrypted multiple times, will produce different ciphertext each time. This obfuscates patterns that attackers might otherwise exploit. It’s like sending messages in code that changes its own cipher with every transmission.
My Take: Is This the Future of Secure Coding?
The project’s creator, who remains somewhat enigmatic, frames this work as a contribution to “Digital Sovereignty and Advanced Privacy.” This is more than just code; it’s a statement of intent in an era where data privacy is becoming a fundamental human right. The “PoetryCoding™ philosophy” mentioned in the P.S.—“code as an act of care. Protect without locking away. Remember without exposing”—resonates deeply. It suggests a vision where security is not an afterthought, but an intrinsic property of well-crafted software.
What’s particularly exciting is the commitment to transparency and adherence to established standards. The code is Apache 2.0 licensed, free for commercial use, and fully testable with over 500 test cases available. This isn’t security through obscurity; it’s security through rigorous implementation and peer-reviewed standards. The planned FIPS 140-3 validation by 2027 signals a serious long-term commitment to meeting the highest security benchmarks, especially for government and regulated industries.
Why Does This Matter for Developers?
For developers, Flash512-Vanguard isn’t just a tool; it’s an enabler. It abstracts away the maddening complexity of cryptographic primitives, allowing them to focus on building features and solving business problems. It empowers smaller teams or individual developers to implement security that was once the exclusive domain of highly specialized security engineers. Imagine building a secure SaaS product, protecting sensitive PII, or encrypting API keys at rest, all with minimal cryptographic overhead. This library makes that vision attainable.
The library is easy to install via pip and has a simple one-time configuration step using an environment variable for its core secret. It’s designed to integrate smoothly into existing workflows, minimizing disruption.
Looking ahead, the roadmap includes hardware security key support and preparation for post-quantum cryptography, indicating a forward-thinking approach to evolving threats. This library isn’t just about solving today’s problems; it’s about anticipating tomorrow’s challenges.
🧬 Related Insights
- Read more: Blockchain Architects: A 4-Book Reading List for First Principles
- Read more: AI Agent Tests Break: Microsoft’s New ‘Trust Layer’ Unveiled
Frequently Asked Questions
What does Flash512-Vanguard actually do? Flash512-Vanguard is a Python library that simplifies the implementation of strong encryption for sensitive data, using standards like AES-256-GCM and Argon2id, and offering automatic memory wiping for enhanced security.
Is Flash512-Vanguard suitable for protecting personal data? Yes, its features like automatic memory wiping, strong KDFs, and AES-256-GCM encryption make it highly suitable for protecting Personally Identifiable Information (PII) and other sensitive user data.
How easy is it to start using Flash512-Vanguard?
It’s designed for ease of use. Installation is a simple pip install flash512-vanguard, and basic encryption/decryption can be achieved with just a few lines of Python code.